Cyber Security Expert
Entry Level Qualification
Class 12
Career Fields
Information Technology & Computer Science
For Specially Abled







Career Entrance Exam
About Career
PARTICULARS | DESCRIPTION |
Name | Cyber Security Expert |
Purpose | Monitoring The Organization's Network |
Career Field | Information Technology & Computer Science |
Required Entrance Exam | JEE ADVANCED |
Average Salary | 300000 - 500000 Rs. Per Year |
Companies For You | BM, Infosys, Tech Mahindra, TCS & Many More |
Who is Eligible | Class 12th Pass |
Cyber Security Experts protect and defend an organization’s or a Government’s or an individual’s computer and networking systems from potential and live cyberattacks which are mostly illegal and fall into the category of cybercrime. Computer and networking systems comprise of computer hardware, operating and application software, networking hardware devices, networking software, intranet (closed internet within a group of people), and internet. Potential threats mean cyberattacks which are likely to happen any time and live means attacks which are happening now.
There are enormous threats of cyberattacks today as we use computer and networking systems for our business, financial, and governance transactions and service delivery. For example, banking network for banking transaction, e-governance sites for delivery of government’s services, online payments, airline reservation systems, and so on. We store personal data online; transact online; billions of gigabytes of data are processed online which comprise of text, audio, and video data.
Cyberattacks can be against a nations’ IT infrastructure that includes telecommunications, energy, Airlines, Banking and Financial networks, transportation, and others. Attackers can disrupt/destroy/misuse these essential services. An attack on the Air traffic control system could wreak havoc with flight schedules; financial and banking systems, when attacked can disrupt a nation’s economy.
There are several types of threats that a computer and networking system may face. Such as:
Threat from malware (viruses, worms, etc.): Malware (malicious software programs) could be file-less which are very difficult to trace or is like a cookie (application software). File-less malware sits directly on the RAM (Random Access Memory of a computer) and reduce the RAM’s speed. There are also malwares called stegware which is hidden within another text, audio, or video file.
Malwares can cripple a system completely or make the system function in a way that the hackers or cyber criminals want. For example, a malware can completely make banking systems go haywire or used to steal data and transfer money.
Data and information theft: These are quite common and easy to do with a malware cookie or a file-less malware. This may also happen through phishing attacks. This is a serious threat as we have a lot of personal and organisational data online; sometimes, all the data of an organisation are online. We have banking passwords, biometric data, etc. While data is processed online, it is at risk from multiple hackers and cyber attackers. A cyber breach can potentially cause loss of valuable and confidential data.
Vulnerability of software: System or operating software as well as application software can have built-in vulnerability to attacks. These are like security holes which could be exploited by hackers and cyber criminals to gain access to computer and networking systems.
DDoS attack: Distributed denial of services. DDoS attacks consume a victim’s network resources in such a degree so that legitimate access to the network is highly affected. For example, if there is a DDoS attack on a e-retail website like Flipkart, legitimate users won’t be able to access.
Phishing attack: Phishing attacks mostly happen through a link sent via email. An unsuspecting user may click on the link and unknowingly download a malware, a trojan virus, or other types of threats such as a ransomware. Phishing attacks may paralyse a computer system, steal data, and even destroy software and hardware.
Meltdown and Spectre: These are vulnerabilities or security holes in microprocessor chips that run your computer and networking hardware. These are quite difficult to track as these bypasses the system and operating software.
Ransomware: Ransomwares are malwares that can completely lock down a computer system. If this attack happens, you cannot just operate your computer. Cyber criminals then ask for a ransom payment. If you pay, then they unlock the system.
APT (Advanced Persistent Threat) attacks: This is a cyberattack which happens on the victim’s computer and network systems over a long period of time without getting detected. The purpose of an APT is often stealing important data and track network/computer activities. APT attacks are often used against a country, say, attacking the defence network and steal sensitive data about a country’s defence infrastructure and plans.
Botnets: A botnet is a set of inter-connected computing devices such as computers, mobile phones, servers, iOT (Internet of Things) devices, etc. The devices under attack are controlled remotely by a malware without the knowledge of the victims. The computing power of the infected devices (such as RAM, Hard drives, etc.) are then used to write malwares for other cyberattacks such as malwares, ransomwares, DDoS, APT, etc.
So, what will you do to protect or defend an organisation, government, or individual from potential and live cyberattacks?
1. The very first thing will be for you to check a computer and networking system’s vulnerabilities or security holes. You will carry out threat analysis and find out potential areas of threats.
2. You will then plan all the system requirements to plug the security holes or vulnerabilities. You will define system access and access control (to thwart the chances of unauthorised access); define requirement of system hardware, firewalls (firewalls are network security systems), anti-virus software, etc. You will install and deploy all these security software across the computer systems and network of an user.
3. Some of the organisation level firewalls in use are Cisco ASA, Barracuda, SonicWall, Juniper, Sophos, HP Fortify, etc. At individual computer level, Windows have a built-in firewall; then you can use AVS, TinyWall, Comodo, etc. You will use anti-virus software like McAfee, Norton, Kaspersky, etc.
4. You will analyse data and information security threats and put in place access control and other security measures. You will plan for recovery from disasters (if a cyberattack happens) and plan how a business can continue during a cyberattack.
5. Depending upon your working hours with an organisation where you work or when you are self-employed, you will keep a vigil on your client organisation’s computer systems and networks. You will detect and thwart any possible cyberattack on the system and network. During a cyberattack, you will fight the attack by deploying various fixes (or software) – which can, let’s say, detect malwares and delete them, recover systems from a DDoS or APT attacks, and plug system vulnerabilities.
Key Roles and Responsibilities
1. As a Cyber Security Expert you would Monitor an organization’s networks for security breaches and investigate a violation when one occurs. Violation or breaches like Fraud and identity theft, Information warfare, Phishing scams, Spam, Propagation of illegal obscene or offensive content.
2. As a Cyber Security Expert you would Install and use software, such as firewalls and data encryption programs, to protect sensitive information.
3. As a Cyber Security Expert you would prepare reports that document security breaches and the extent of the damage caused by the breaches.
4. As a Cyber Security Expert you would perform advanced level of security investigation on following areas: application security, cloud security, data security, network security and perimeter security
5. As a Cyber Security Expert you would research the latest information technology (IT) security trends.
6. As a Cyber Security Expert you would modify computer security files to incorporate new software, correct errors, or change individual access status.
7. As a Cyber Security Expert you would review violations of computer security procedures and discuss procedures with violators to ensure violations are not repeated.
8. As a Cyber Security Expert you would monitor use of data files and regulate access to safeguard information in computer files.
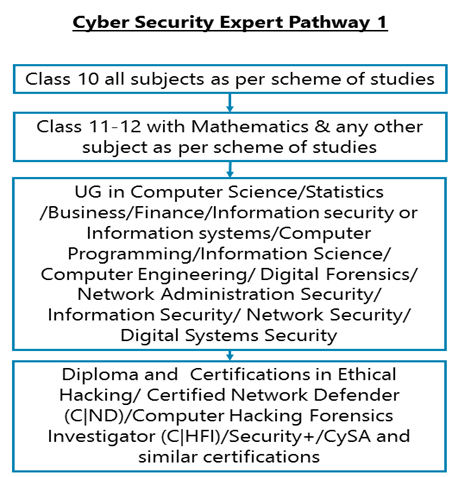
Career Entry Pathway
Class 10 all subjects as per scheme of studies – Class 11-12 with Mathematics & any other subject as per scheme of studies – UG in Computer Science/Statistics /Business/Finance/Information security or Information systems/Computer Programming/Information Science/ Computer Engineering/ Digital Forensics/ Network Administration Security/ Information Security/ Network Security/ Digital Systems Security – Diploma and Certifications in Ethical Hacking/ Certified Network Defender (C|ND)/Computer Hacking Forensics Investigator (C|HFI)/Security+/CySA and similar certifications
After completing Class 11-12 with Mathematics & any other subject as per scheme of studies you can go for an undergraduate degree in Computer Science/Statistics /Business/Finance/Information security or Information systems/ Information Technology / Computer Programming/ Information Science/ Computer Engineering / Digital Forensics/ Network Administration Security/ Information Security / Network Security/ Digital Systems Security. After having completed graduation in any of the above disciplines, you can also go for Diploma courses in Cybersecurity or you can go for various Professional certifications in Cybersecurity such as: Certified Ethical Hacker (CIEH), Certified Network Defender (C|ND), Computer Hacking Forensics Investigator (C|HFI), Security+, DSCI certified Privacy Lead assessor DCPLA course among many others. Professional certifications like Certified Ethical Hacker (CIEH), Certified Network Defender (C|ND), Computer Hacking Forensics Investigator (C|HFI), Security+, DSCI certified Privacy Lead assessor DCPLA are earned through examination process. After clearing examination from the respective examining bodies, the candidate becomes a certified professional.
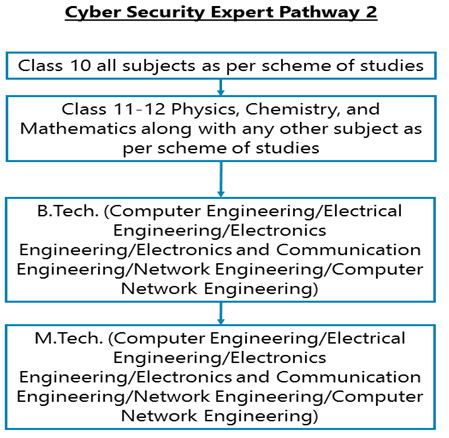
Class 10 all subjects as per scheme of studies – Class 11-12 Physics, Chemistry, and Mathematics along with any other subject as per scheme of studies – B.Tech. (Computer Engineering/Electrical Engineering/Electronics Engineering/Electronics and Communication Engineering/Network Engineering/Computer Network Engineering) – M.Tech. (Computer Engineering/Electrical Engineering/Electronics Engineering/Electronics and Communication Engineering/Network Engineering/Computer Network Engineering)
After completing Class 11-12 Physics, Chemistry, and Mathematics along with any other subject as per scheme of studies you can pursue graduation in B.Tech. In Computer Engineering/Electrical Engineering/Electronics Engineering/Electronics and Communication Engineering/Network Engineering/Computer Network Engineering or similar discipline. After a graduation degree in B.Tech you can go for M.Tech. In the similar field.
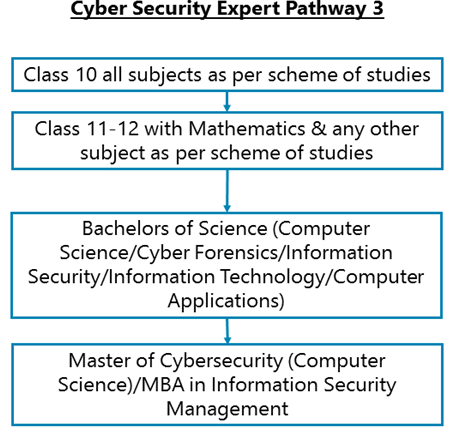
Class 10 all subjects as per scheme of studies – Class 11-12 with Mathematics & any other subject as per scheme of studies – Bachelors of Science (Computer Science/Cyber Forensics/Information Security/Information Technology/Computer Applications) – Master of Cybersecurity (Computer Science)/MBA in Information Security Management
After completing Class 11-12 with Mathematics & any other subject as per scheme of studies, you can go for a Bachelor’s of Science in Computer Science/Computer Engineering/Cyber Forensics/Information Security/Information Technology/Computer Applications or similar courses. Then you can pursue a master’s degree in Cybersecurity or an MBA in Information Security Management or related field.
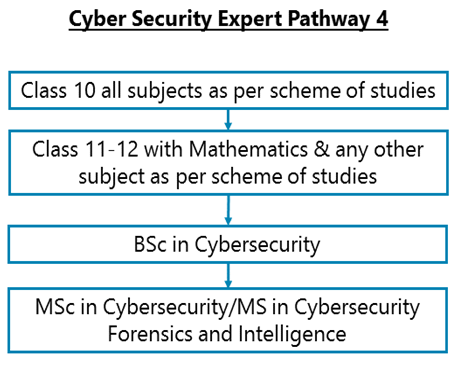
Class 10 all subjects as per scheme of studies – Class 11-12 with Mathematics & any other subject as per scheme of studies – BSc in Cybersecurity – MSc in Cybersecurity/MS in Cybersecurity Forensics and Intelligence
After having completed Class 11-12 with Mathematics & any other subject as per scheme of studies you can go for a BSc in Cybersecurity. After a graduation degree in Cybersecurity, you can pursue a Master’s of Science in Cybersecurity or MS in Cybersecurity Forensics and Intelligence.
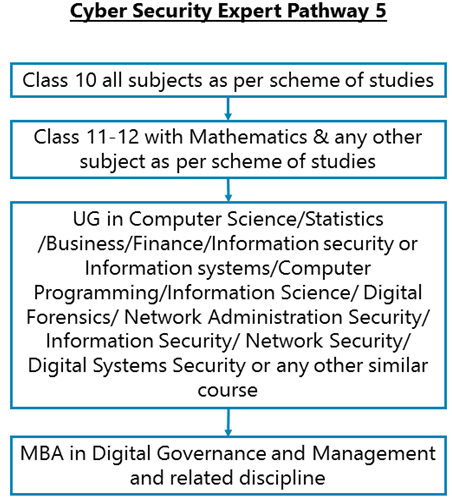
Class 10 all subjects as per scheme of studies – Class 11-12 with Mathematics & any other subject as per scheme of studies – UG in Computer Science/Statistics /Business/Finance/Information security or Information systems/Computer Programming/Information Science/ Digital Forensics/ Network Administration Security/ Information Security/ Network Security/ Digital Systems Security or any other similar course – MBA in Digital Governance and Management and related discipline
After having completed Class 11-12 with Mathematics & any other subject as per scheme of studies you can go for a Bachelor’s degree in Computer Science/ Statistics /Business/ Finance/ Information security or Information systems/ Information Technology/ Computer Applications / Computer Programming/Information Science/ Digital Forensics/ Network Administration Security/ Information Security/ Network Security/ Digital Systems Security or any other similar course. Then you can do an MBA in Digital Governance and Management or a similar course.
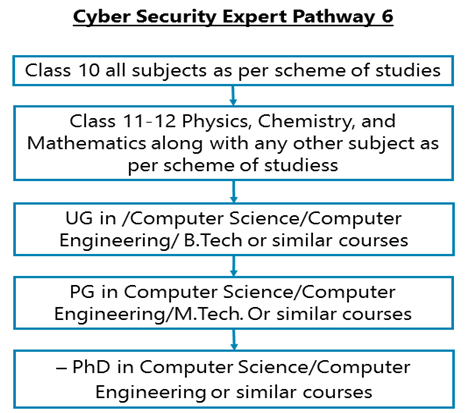
Class 10 all subjects as per scheme of studies – Class 11-12 Physics, Chemistry, and Mathematics along with any other subject as per scheme of studiess – UG in /Computer Science/Computer Engineering/ B.Tech or similar courses – PG in Computer Science/Computer Engineering/M.Tech. Or similar courses – PhD in Computer Science/Computer Engineering or similar courses
After completing Class 11-12 Physics, Chemistry, and Mathematics along with any other subject as per scheme of studies, you can go for undergraduate course in Computer Science/Computer Engineering/B.Tech. Or similar courses. You can then pursue a masters in Computer Science/Computer Engineering or M.Tech with specialisation in cyber security. After having completed you masters you can go for a PhD with specialisation in Cybersecurity or related discipline.
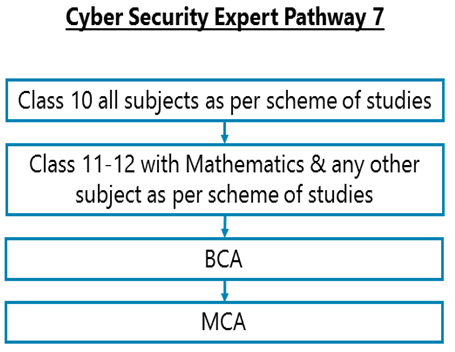
Class 10 all subjects as per scheme of studies – Class 11-12 with Mathematics & any other subject as per scheme of studies – BCA - MCA
After completing Class 11-12 with Mathematics & any other subject as per scheme of studies you can go for a graduate degree in BCA. After a graduation in BCA you can then go for masters in the same field i.e. MCA. Remember that there are some colleges which offer BCA courses even if you don’t have Mathematics in Class 11-12.
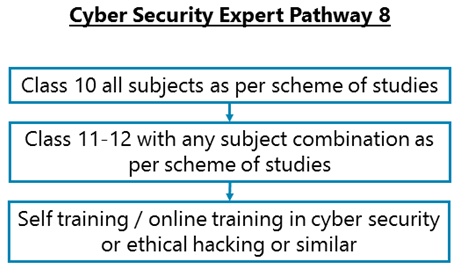
Class 10 all subjects as per scheme of studies – Class 11-12 with any subject combination as per scheme of studies – Self training / online training in cyber security or ethical hacking or similar
After completing Class 11-12 with any subject combination as per scheme of studies you can enrol in online training courses in either cyber security or ethical hacking or similar training courses. You can go for online cyber security courses such as: Certified Ethical Hacker, Computer hacking Forensics Investigator, EC-Council Certified Security Analyst, and Certified Secure Computer User among many others.
Required Qualification & Competencies
After completing higher secondary education with Mathematics along with any other subject as per scheme of studies, you can go for a Bachelor’s in Computer Science / Statistics / Business/ Finance/ Information security or Information systems/ Computer Programming/ Information Science/ Information Technology/ Computer Applications / Digital Forensics/ Network Administration Security/ Information Security/ Network Security/ Digital Systems Security followed by a Post-Graduate Diploma in Cybersecurity.
After completing higher secondary education Mathematics along with any other subject as per scheme of studies, you can for a BSc in Cybersecurity followed by a masters in the same field.
After completing Higher Secondary Education with Physics, Chemistry and Mathematics along with any other subject as per scheme of studies, you can go for a Bachelor’s degree in Engineering (Computer science/ Electrical/ Computer Engineering) followed by master’s degree in Cybersecurity or an MBA in Information Security Management or related field.
After completing Higher Secondary Education with any subjects you can directly start taking online training in cyber security. Online courses such as: Certified Ethical Hacker, Computer hacking Forensics Investigator, EC-Council Certified Security Analyst, and Certified Secure Computer User among many others can help you gain more experience in this field.
There are professional Diploma/certification courses in Cybersecurity such as: CompTIA Security +, Operating System Security, Computer Forensics, Security Procedures and Network Security Application Encryption and Fundamentals of information security.
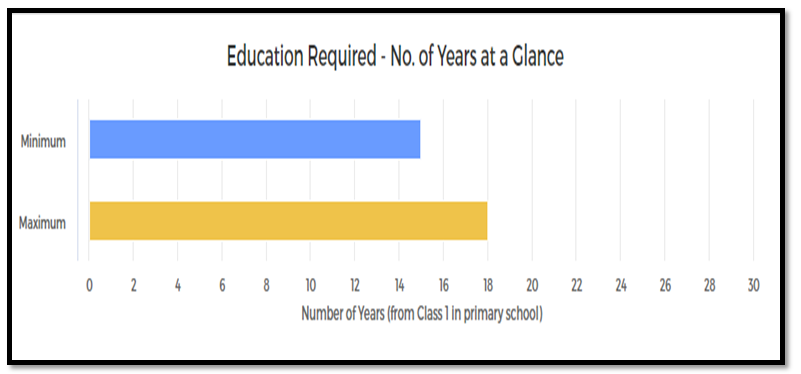
MINIMUM EDUCATION REQUIRED | MAXIMUM EDUCATION REQUIRED |
Under Graduate Undergraduate Degree / Honours Diploma / Graduate Diploma (equivalent to a Degree) Programs for which the minimum eligibility is a pass in Higher Secondary / Class XII School Leaving examination. | Post Graduate Postgraduate Degree / Diploma / Certificate Programs for which the minimum eligibility is a pass in Graduation / equivalent Diploma program like Honours Diploma or Graduate Diploma. |
COMPETENCIES REQUIRED
Interests
1. Investigative: You should have interests for Investigative Occupations. Investigative occupations involve working with ideas and quite a lot of thinking, often abstract or conceptual thinking. These involve learning about facts and figures; involve use of data analysis, assessment of situations, decision making and problem solving.
2. Realistic: You should have interests for Realistic Occupations. Realistic occupations involve more practical and hands-on activities than paperwork or office work. Realistic occupations often involve physical activities for getting things done using various tools and equipment.
3. Enterprising: You should have interests for Enterprising Occupations. Enterprising occupations involve taking initiatives, initiating actions, and planning to achieve goals, often business goals. These involve gathering resources and leading people to get things done. These require decision making, risk taking and action orientation.
Abilities
1. Abstract Reasoning: The ability to understand ideas which are not expressed in words or numbers; the ability to understand concepts which are not clearly expressed verbally or otherwise.
2. Deductive Reasoning: The ability to apply general rules to specific problems to produce answers that make sense.
3. Inductive Reasoning: The ability to combine pieces of information to form general rules or conclusions (includes finding a relationship among seemingly unrelated events)
4. Numerical Reasoning: The ability to add, subtract, multiply, divide, and perform other basic numerical calculations correctly.
5. Problem Sensitivit: The ability to tell when something is wrong or is likely to go wrong. It does not involve solving the problem, only recognizing there is a problem.
6. Information ordering: The ability to arrange things or actions in a certain order or pattern according to a specific rule or set of rules (e.g., patterns of numbers, letters, words, pictures, mathematical operations)
Skills
1. Active Learning: Focused and continuous learning from various sources of information, observation and otherwise for application in getting work done.
2. Communication in English: Skills in communicating effectively in writing as well as verbally with others in English language.
3. Computer (Software Development): Skills in using programming languages such as C, C++, Python, Java, Ruby, Swift, Perl, LISP, and SQL; development tools such as GitHub, Bootstrap, Dreamweaver, Atom, etc.; operating systems such as Windows 10, Linux, Android, Ubuntu, Mac OS, DOS, Unix, etc.; and project management tools such as Agile and SCRUM.
4. Computer (Web Authoring and Development Tools): Skills in using HTML, PHP, Adobe Dreamweaver, JavaScript, jQuery, CSS, etc. as well as different web content management systems such as WordPress, Joomla, and Drupal.
5. Critical Thinking: Skills in analysis of complex situations, using of logic and reasoning to understand the situations and take appropriate actions or make interpretations and inferences.
6. Judgment and Decision Making: Skills in considering pros and cons of various decision alternatives; considering costs and benefits; taking appropriate and suitable decisions.
7. Problem Solving: Skills in analysis and understanding of problems, evaluating various options to solve the problems and using the best option to solve the problems.
8. Programming: Skills in writing computer programs for various applications, installation of computer programs and troubleshooting of problems in computer programs or software.
9. Reading Comprehension: Skills in understanding written sentences and paragraphs in work related documents.
10. Technical: Skills in using various technologies and technical methods to get things done or solve problems.
11. Time Management: Skills in prioritizing work, managing time effectively.
12. Troubleshooting: Skills in determining causes of operating errors and deciding what to do about it.
Knowledge
1. Computers: Knowledge of computer hardware and software, computer programming, computer networks, computer and mobile applications.
2. Cyber security testing and protection tools: Knowledge of various tools used in cyber security testing such as Metasploit, Nmap, Wireshark, Nessus, Burpsuite, Nikto, Netsparker Security Scanner, Acunetix, WebTitan, Log360, John The Ripper, GNU PG, ClamAV, OpenVAS, BackTrack, Qualys, Okta, Cipher Cloud, Cryptosense, Trend Micro Cloud App Security, SiteLock, etc.
Personality
1. You are somewhat organised in your day-to-day life and activities.
2. You are somewhat careful about your actions and behaviour.
3. You are somewhat disciplined in your action and behaviour.
4. You remain calm in difficult situations sometimes but some other times you are anxious.
5. You are imaginative sometimes.
6. You prefer to experience new things and have new experiences sometimes.
7. You act independently sometimes but do not do so in some other times.
8. You are friendly and outgoing sometimes, but not always.
9. You prefer company of people sometimes but not always.
Career - Job Opportunities & Profiles
As a graduate or a Post-Graduate in Computer science or related field, you can find job opportunities initially as a Cyber Security Analyst / Application Security Analyst / Information Security Analyst / Data Security Analyst / or in similar roles in different types of organisations – right from IT Software and Services companies, Computer / Network hardware companies and not-for-profit companies to Government departments and public services companies. Following are some of the various types of organisations where you can find jobs:
1. IT software and services companies like IBM, Infosys, Tech Mahindra, TCS, Cognizant Technology Solutions, Wipro, etc.





2. IT hardware and networking equipment manufacturing and servicing companies like Intel, Qualcomm, Cisco, Dell, HP, Lenovo, Samsung, Sony, etc.


3. IT department of any corporate organisation such as Tata Steel, Reliance Industries Limited, ITC, Hindustan Unilever, SAIL, L&T, etc.


4. IT departments of banks and financial institutions such as State Bank of India, ICICI Bank, LIC, Goldman Sachs, JP Morgan Chase, etc.



5. Telecommunication and Data Service Providers such as Reliance Jio, Airtel, Vodafone, etc.



6. Non-Profit Organizations or Government initiated programmes such as: Data Security Council of India (DSCI), National Cyber Security Coordinator (NCSC), Indian Computer Emergency Response Team (CERT-In), National Critical Information Infrastructure Protection Centre (NCIIPC), Cyber Swachhta Kendra (Botnet Cleaning and Malware Analysis Centre), National Cyber Coordination Centre (NCCC), and Cyber Crime Prevention for Women and Children (CCPWC) - at the beginning, you will get appointed as an Intern or a trainee or an Associate or similar position.
7. Non-Profit International Organizations such as: ISACA, ISF - Information Security Forum, Centre for Internet Security, OWASP - The Open Web Application Security Project, WiCyS - Women In Cybersecurity,
8. Government launched Independent Business Divisions like National e-Governance Division (NeGD) under Digital India Corporation – at the beginning, you will get appointed as Project Manager/ Program Manager under various e-governance projects like Unified Mobile Application for New-age Governance (UMANG), Digi Locker, Program Management Information System (PMIS) among many others.
9. All private sector organizations such as: The SANS Institute, ISSA - Information Systems Security Association, Internet Security Alliance, Cyber, Space & Intelligence Association, National Cyber Security Association, Cybersecurity and Infrastructure Security Agency (CISA) and other International organizations where you can begin as a volunteer or an intern. Or Security Administrator.
SPECIALISATION TRACKS IN THIS CAREER
1. Information Security Expert
Information Security Experts analyse an organisation’s or government’s computer and networking infrastructure to detect vulnerabilities and suggest measures – at hardware, software, and network level to plug the vulnerabilities. They implement solutions, install security software, and test systems. They find out vulnerabilities of data and information thefts and implement systems and solutions to thwart the theft possibilities.
2. Network Security Expert
Network Security Experts are specialist in detecting, preventing, protecting, and defending threats to an organisation’s networking systems, intranet, and internet. They find out vulnerabilities and implement solutions to make the networks safe from cyberattacks.
3. Application Security Expert
Application Security Experts are responsible for the detection, protection, and defence of various application software from threats of cyberattacks. Applications could range from a simple app on your mobile phone to a complex application which runs airline reservation system.
4. Data and Information Security Professional
Data and Information Security Professionals are involved in providing consultation regarding security awareness, ongoing access management, risk assessment and data classification issues to the organizations. They also monitor the resolution of audit recommendations and information system security risks.
5. Forensic Cyber Analyst
Forensic Cyber Analysts are involved in investigating data breaches, security incidents and criminal activity in the cyber space. They review and analyse data linked to cybercrimes such as network infringement, hacking, online fraud, political, industrial and commercial spying, terrorist communication, and theft of confidential information.
6. Ethical Hacker
Ethical Hackers are professional hackers employed by organizations to penetrate or access networks and computer systems in order to fix and find security data breaches and vulnerabilities. Ethical Hackers are recruited by many country’s and state’s Government as well as police and armed forces to hack into enemy country’s computer and information systems and networks as well as into those of terrorist/criminal organisations or individual terror suspects and criminals. They also hack into the mobile phones of people who are identified as threat to the national security of a country or alleged to be involved in terror or criminal activities. Though this is quite controversial, but today, most countries’ Government and law and order machinery employ Ethical Hackers to listen to conversations on the internet, mobile phone, and on the dark web (dark web runs on the internet but common search engines and users cannot access normally; access requires specific software and authorisation to access).
7. Penetration Tester
Penetration Testers are authorized professionals who perform simulated cyberattacks to evaluate and analyse the security of the systems of an organisation. They tend to find the sources of breach and identify vulnerabilities and system strengths.
CAREER GROWTH
You will begin your career as a Cyber Security Analyst / Data Security Analyst / Information Security Analyst / in a similar position.
After this level, your career progression, could be as given below depending upon your experience, expertise, and work performance:
Senior Analyst – Lead Analyst – Security Architect / Solution Architect / similar – Consultant – Vice President – President
There are various other mid and senior level positions as well. In some organisations, you will progress as:
Senior Analyst – Lead Analyst – Associate Consultant – Consultant – Senior Consultant – Vice President – President
In some corporate organizations, you will progress as:
Analyst – Assistant Manager – Manager – Senior Manager – Assistant Vice President – Associate Vice President – Vice President – Chief Information Officer.
Salary Offered
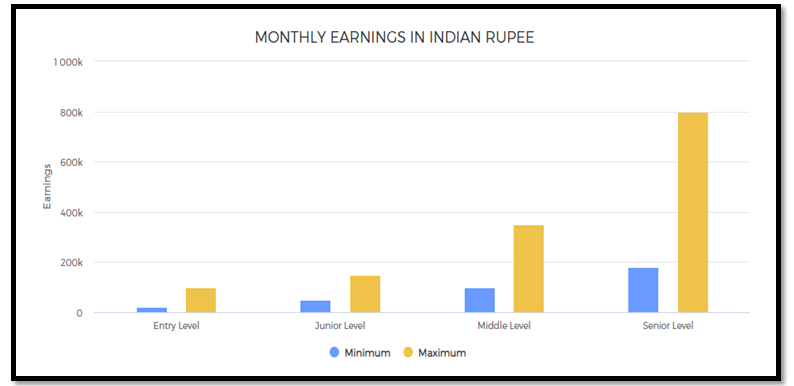
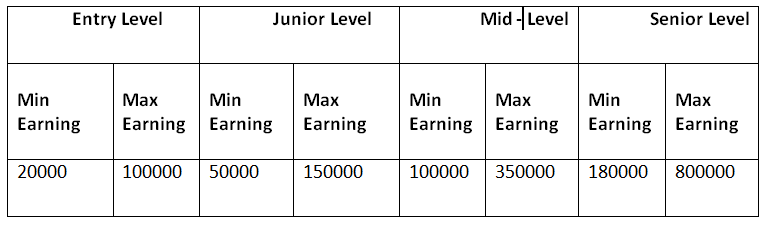
As you may get a job in this field in different roles depending upon your qualifications and expertise, salaries vary widely.
In India:
1. At the beginning of your career, as an Analyst with 0-1 year of experience, you may expect to get about Rs. 20,000 to 45,000 or more per month. If you are passing out from a premier engineering college, you may get about Rs. 1,00,000 or even more per month.
2. At a junior level with experience of 1-4 years, depending upon your expertise, you may get about Rs. 50,000 – 1,50,000 or even more per month.
3. Mid-level salaries (with 5-12 years of experience) may vary from Rs. 1,00,000 – 3,50,000 per month or even more.
4. At senior level (with 12-20 years of experience), you may earn about Rs. 1,80,000 – 8,00,000 or even more a month. Chief Information Officers may earn about Rs. 50,00,000 to 3,00,00,000 or much more per year.
In US:
1. At Entry level as an Intern or Trainee, you may earn about $ 4,000 - $7,000 per month.
2. At Junior-level, with an experience of 1-5 years, you may earn around $ 5,000 - $ 11,500 or more per month.
3. At Mid-level, with an experience of 6-12 years, you may earn around $ 6,500 - $ 14,500 per month.
4. At Senior-level, with an experience of 13-20 + years, you may earn around $ 8,500 - $18,000 per month.
MONTHLY EARNINGS IN INDIAN RUPEE
1. Entry level: 0 - 2 years of work experience
2. Junior Level: From 1 to 12 years of work experience
3. Mid Level: From 5 to 20+ years of work experience
4. Senior Level: From 10 to 25+ years of work experience (there could be exceptions in some high-end technical, financial, engineering, creative, management, sports, and other careers; also in the near future, people will reach these levels much faster in many careers and in some careers, these levels will have no meaning as those careers will be completely tech skill driven such as even now, there is almost no level in a Cyber Security Expert’s job)
Work Activities
1. Analyzing and interpreting data and information: Analysis of data and information to find facts, trends, reasons behind situations, etc.; interpretation of data to aid in decision making.
2. Computing: Computing using various computer software applications; writing algorithm for various computer and mobile applications; using software applications for scientific and technical work.
3. Decision making and problem solving: Analysis of data and information; evaluation of alternative decisions and results of decisions; taking the right decisions and solving problems.
4. Getting Information and learning: Observing, hearing, reading, using computers, or otherwise obtaining information and learning from it.
5. Processing of information: Searching, compiling, and tabulating, calculating, auditing, verifying or otherwise dealing with information processing including data entry, transcription, recording, storing and maintaining databases.
6. Monitoring processes, systems and performance: Observing and recording information on various criteria to monitor mechanical, electronics, electrical and other processes and systems; monitoring progress of projects and tasks.
7. Organizing, planning and prioritizing tasks: Planning and organizing tasks in order to achieve work goals; prioritizing tasks to achieve goals and making the best use of the time available.
8. Strategic planning: Developing visions and goals, developing strategies and action plans for achieving visions and goals.
9. Using computers for work: Using computers for day-to-day office work; using computer software for various applications in day-to-day professional work; entering data and process information; for writing.
10. Working with computers, programming and performing technical tasks: Using computers and computer systems, both hardware and software for programming, developing software and / or hardware, developing computer applications, systems, and networks; developing mobile applications.
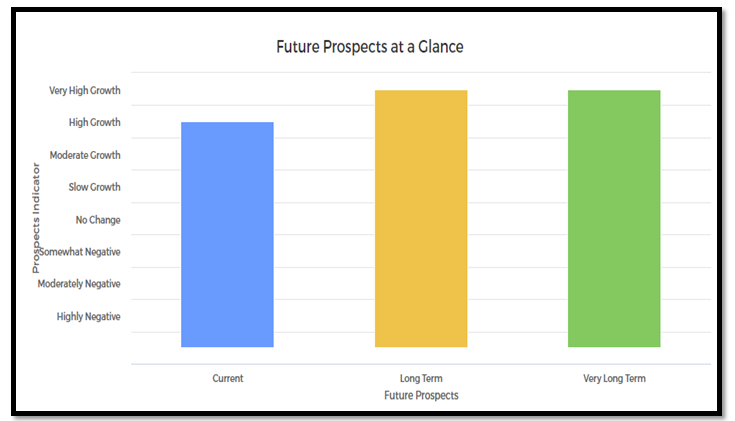
Future Prospects
You can expect an exciting future in this field. BeyondTrust, a leading cyber security firm, has predicted Internet of Things (IoT) to become one of the major targets of hackers in the coming years. Since the Internet of Things devices like smart TVs, smart speakers, smart watches, appliances and many others are not built with cyber security in mind and these smart gadgets can be exploited and manipulated very easily. It was also estimated that around 50% of the cyber-crimes are generated through Email spamming.
According to the World Economic Forum, almost 85% of the companies are likely to expand their adoption of user and entity and big data analytics and will be making extensive use of cloud computing.
There’s already a shortage of security skills today, and this will only get worse in the coming years based on data being provided from universities. Organizations are struggling to fill gaps by cross training IT workers, but that’s simply not enough given the sheer volume of applications, data, devices, infrastructure and people that require protecting and defending. Cybersecurity experts are needed in organizations and industries like healthcare and retail, which have been hit hard by Cybercrime. Therefore career in Cyber security has ample opportunities.
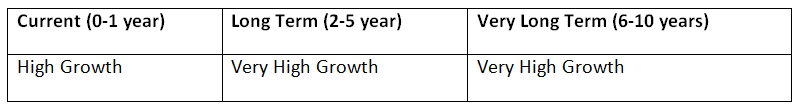
FUTURE PROSPECTS AT A GLANCE